Counterterrorism and Cybersecurity
(税込) 送料込み
商品の説明
Counterterrorism and Cybersecurity
Total Information Awareness
Newton Lee
Provides a broad survey of the United States counterterrorism and cyber security history, strategies and technologies
Demystifies Total Information Awareness and Edward Snowden"s NSA leaks
Examines U.S. intelligence community, causes and cures for terrorism, war and peace, cyber warfare and cyber security in healthcare and everyday life
Discusses artificial intelligence in data mining, penetration testing, USB write-blocking and forensics, and DARPA"s $2 million Cyber Grand Challenge
64.99Euro/(アマゾン)商品の情報
| カテゴリー | 本・音楽・ゲーム > 本 > 洋書 |
|---|---|
| 商品の状態 | 未使用に近い |

Counterterrorism and Cybersecurity: Total Information Awareness

Counterterrorism and Cybersecurity: Total Information Awareness

Counterterrorism and Cybersecurity by Newton Lee, Hardcover

Cyber Security as Counter-Terrorism: Seeking a Better Debate - War

Cybersecurity and New Technologies | Office of Counter-Terrorism

Counterterrorism | National Counterterrorism Innovation

Cybersecurity and New Technologies | Office of Counter-Terrorism

Questions of ethics arise as Google cybersecurity report exposes

Applying Counterterrorism Strategies to Ransomware - Chainalysis

FBI agent: Cracking the Code: A Glimpse into the World of FBI

What cyber can learn from counterterrorism - Nextgov/FCW

For the latest in COUNTERTERRORISM & CYBERSECURITY NEWS, read this

Can Anything Stop Cyber Attacks? - Knowledge at Wharton

All courses | UNOCT LMS

Dept. of Homeland Security releases new counterterrorism strategy
Navigating the Nexus: Cybersecurity, Counterterrorism, and the

NJ Homeland Security on X:

NJ Homeland Security on X:

Cybersecurity and New Technologies | Office of Counter-Terrorism

We are proud to announce that our Master of Counterterrorism has

NJOHSP on LinkedIn: For the latest in COUNTERTERRORISM

Counterterrorism Tradecraft in Advanced Persistent Threat
Applying AI Techniques in Cybersecurity, Counterterrorism, and

Counterterrorism and Cybersecurity: Total Information Awareness

Cybersecurity is the New Counterterrorism: Experts Examine

Post-9/11 Counterterrorism Should Be Model for Cyber Infrastructure
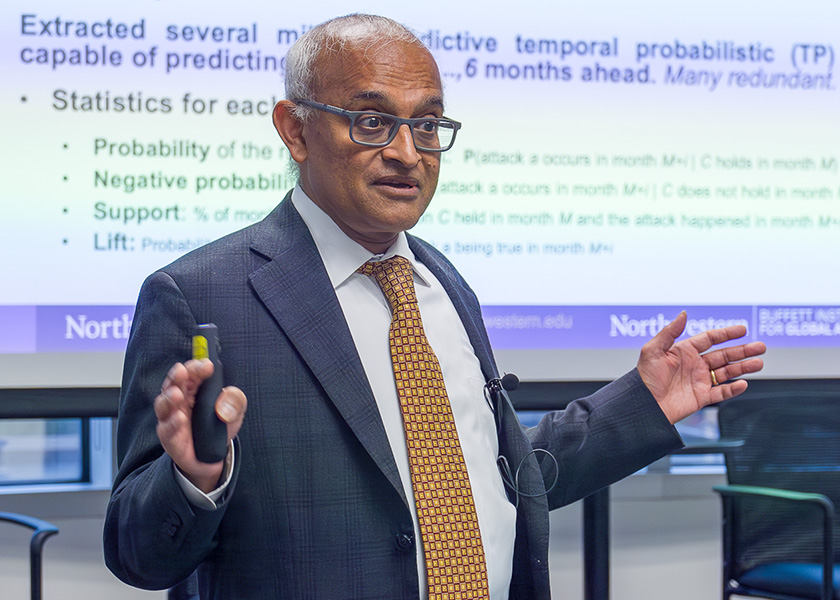
Advancing AI Systems in Cybersecurity, Counterterrorism, and

Counter-terrorism projects

New Jersey Office of Homeland Security and Preparedness - Wikipedia

Applying AI Techniques in Cybersecurity, Counterterrorism, and
Counterterrorism and Cyber Security

What Jobs Can You Get With a Degree in Cybersecurity? - Nichols

United Nations Office of Counter-Terrorism on X:
Protecting Critical Infrastructure from Terrorists' Cyber-Attacks

Advancing AI Systems in Cybersecurity, Counterterrorism, and
Cybersecurity and New Technologies | Office of Counter-Terrorism

V.S. Subrahmanian on LinkedIn: #ai #counterterrorism #ai
PDF | Counterterrorism Lessons for Cybersecurity: How a Decade's

Cybersecurity

IBI CYBERPOL — Bureau International de Cyber Sécurité

商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています














